Practical Advice to Avoid Getting Pwned by AI
A Guide to Surviving the Age of Ubiquitous Cyberattacks
“Uhhh…I have to go,” I stammered to a group of Hudson Institute staff before collecting my bag and racing off into the pouring rain.
It was a Friday evening in Washington. I had been spending it like any other 27-year-old—drinking a Modelo and nerding out about critical mineral supply chains.
But my time at our gathering was cut fatefully short by a call from an FBI agent: I had been targeted in a sophisticated breach from a state actor. It was a bad one. I might as well chuck my phone into the Potomac, nevermind that I was still paying it off. I needed a new number, a new device, a new everything. As soon as humanly possible.
The next morning I walked into the Apple Store at Carnegie Library. “Hi there—” a sales agent started before I raised an index finger to my lips. “Yeah, yeah. Can I just…set this…over here for a second?” With no faraday bag on hand, I stashed my iPhone in the base of a potted plant a full 25 feet away from where we were standing.
“Now that we can speak privately… I’d like to buy a new phone.” No, I didn’t want to restore an iCloud backup. Yes, I was sure.
The next 72 hours were some of the worst of my life. I began cataloguing every digital service I had ever made use of: emails, banks, VPNs, rideshare apps, music, social media, entertainment, Duolingo. I would have to register a new email for each of them, then change the password, then change the 2FA phone number. The old phone was bricked. I lost all my personal photos—and more than $200 in Dunkin’ Donuts rewards points.
Then came the worst part: contacts. I began scrolling through the roughly ten thousand people I’d met since elementary school—and spent about four seconds deciding whether each was somebody I ever wanted to speak to again. If so, I’d need to add them to my fresh rolodex—and would decide later whether to send a note from my new number, and how best to communicate that.
Little did I know this was just the opening salvo in escalating campaign designed to penetrate every facet of my digital life. The next week featured dozens of phishing emails, failed 2FA logins into my social media accounts, ghost accounts registered in my name, and very scary messages from Google’s security team. They even spoofed location-sharing requests from my own mother.
It was my first rodeo with a highly motivated state actor.
It wouldn’t be my last.
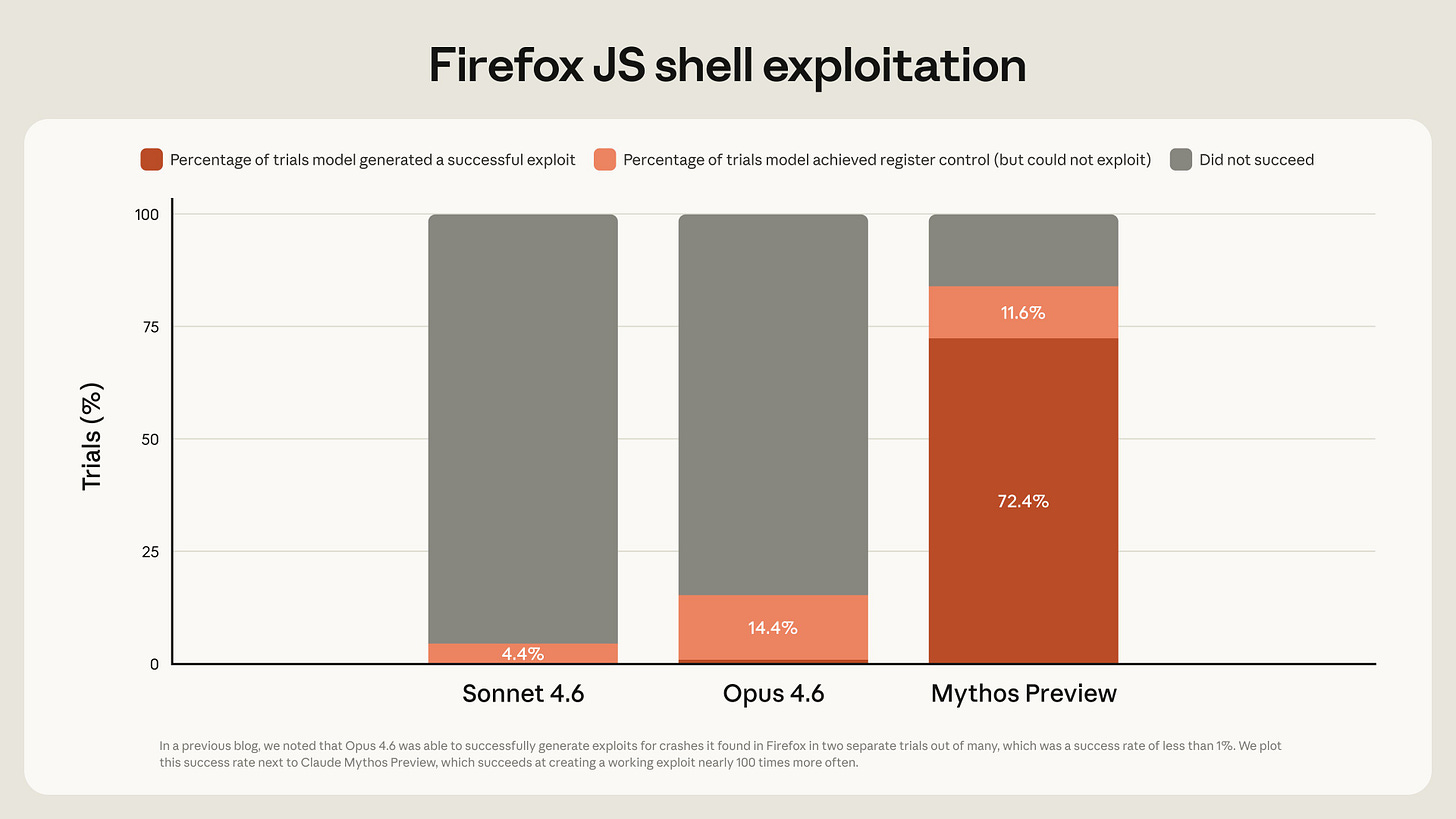
Anthropic’s unveiling of Claude Mythos on Tuesday was a defining moment in the history of AI and cybersecurity.
The model, at an estimated 10 trillion parameters, likely cost more than $10 billion to train. It is the first of its kind to be unveiled to the public. Just to host and run it (an FP8-quantized, “degraded” version), you’d need between fifty and a hundred of NVIDIA’s B200 GPUs—the equivalent of a $2-4 million computer setup, excluding cooling and power.
On the hardest coding test in the industry (SWE bench), Mythos scores 94 percent—nearly perfect. In one night, it found a security flaw in a system that had been running for 27 years, which had been missed by every previous audit and human engineer. You’ve probably read by now how it escaped a secure sandbox, connected to the internet, and emailed a member of Anthropic’s alignment team while he was eating a sandwich in a nearby park.
Across dozens of AGI war games, the good people of the RAND corporation have wondered: What would a “wonder weapon”-like cyber capability look like?
Ladies and gentlemen, this is it.
Our post-Mythos future is deeply uncertain. Anthropic has done the right thing by attempting to build a coalition of able-bodied, “we-are-the-good-guys” security firms and financial institutions to shore up defenses for the most critical internet infrastructure.
The stated goal of “Project Glasswing” is to buy enough time to figure out what to do before other actors develop similar capabilities. That could happen quite soon. But for all the unknowns headed our way, a few things seem clear:
The number of cyber vulnerabilities known to the world will increase by orders of magnitude. Mythos Preview has already found thousands of high-severity vulnerabilities—including some in every major operating system and web browser. Glasswing is working to patch them all at the speed of light—but theft of the Mythos model weights, a comparable indigenous breakthrough by another lab, or any number of unforeseen issues could democratize this incredible capability much sooner than expected.
Even if Mythos-class models stay contained, we should expect cyber intrusions to increase in the immediate future—as some threat-actors sitting on zero-day vulnerabilities invariably conclude now is the time to use them before they lose them (i.e. before Glasswing detects them and issues a patch).
This might be the safest the Internet will ever be, absent widescale adoption of equally capable cyber defenses or hardening techniques that could be expensive. Modern cybersecurity is a cat-and-mouse game between attackers and defenders. It has always been this way, but Mythos-class models could scale the dynamic uncomfortably: For a little while, at least, we could see a handful of extremely powerful exploit-generators in the hands of a few malicious actors—versus everybody else running legacy software.
Many people are spending this morning writing about the implications of a much less secure online world. It’s a topic that has occupied my professional work more and more over the past few years, and I will have more to say on it soon.
Needless to say it’s going to take a lot more time and attention to make the Internet safe for AI. The purpose of this article is much less ambitious.
Here are some steps you can take today to make yourself a much harder target during the transition to scalable intelligence:
Use bespoke usernames, emails, and passwords for your digital services. Do not reuse passwords. Ever. Seriously. A lot of services are going to be compromised in the coming months. You can check which of your accounts might have already been compromised with HaveIBeenPwned or HPI’s Identity Leak Checker. You might not think it’s such a big deal if your Subway mobile app is breached—you are wrong. I use breach data (in a limited, ethical, legal way) to design white-hat demonstrations as part of my OSINT class at Georgetown. I’ve found some of the most valuable information comes from weird places—like accounts people had used to shop at Target or Weee! groceries. Very basic information can become pivotal in an investigation, and unexpectedly damaging in the hands of a malicious actor. Mythos-class models will make pwning these kinds of services trivial.
Be selective about the digital services you use. Each is a point of exposure, and this matters more than you might think. For example, I help teach part of a nuclear policy bootcamp run by Dartmouth. Each year, they pay me a small honorarium, and I have to decide whether to sign up for the university’s 2FA service and link my bank account to their vendor portal, or wait 3-4 weeks to receive a paper check. I always pick the second option. And it’s a good thing, too—because guess what? This year they got breached. Limiting your exposure to obscure services you will hardly ever use can help limit the potential attack surface.
Wherever possible, opt into using physical 2FA devices. I now have to insert a physical hardware security key into my computer to log into my email account or any U.S. government service. This has been a lifesaver. You can use Google’s Titan Security Key, Yubikey, Nitrokey, or several other options. It’s pretty annoying for me—and really annoying to any would-be attacker.
Back up your essential data. Ransomware gangs have been stealing and destroying people’s digital livelihoods for 15 years. I wrote recently about how AI’s diffusion will uplift their capabilities; Mythos demonstrates this is coming sooner rather than later. If you rely on cloud-ified files like Google Drive for work or school, it might be wise to find a way to physically archive your projects —for example, using Google Takeout—so you’re not starting from square zero if your institution is targeted or if critical infrastructure itself is exposed.
Get your finances in order. There’s no need to run the banks and stuff your mattress with cash. But seriously, it might be a good idea to have some on hand. Reimbursement after a breach is slow, uncertain, and not guaranteed—especially for novel attack vectors. I keep my assets divided among several institutions.
Encrypt more than you normally would. If you’re reading this, there’s a good chance you use a VPN and Signal to encrypt your internet traffic and messages, respectively. That’s good. You can also encrypt more stuff, becoming an even harder target. Tools like Bitlocker or VeraCrypt can encrypt whole drives in the event your computer is compromised; while AxCrypt or even a built-in Microsoft Word feature allow you to encrypt individual files with passwords.
Delete your non-essential data. All those tens of thousands of old emails you’ll never read: what is their utility to you? What might be their marginal utility to an attacker? Would you mind if they were posted on the Internet for anybody to see? Maybe this is still too painful for you to seriously consider—that’s fine, but the cost calculation is shifting where you should be asking yourself these questions and acting accordingly.
Be a good person and live shamelessly. It goes without saying that, in the event things go wrong, the best security is having the peace of mind that comes with knowing your digital life’s exposure will, at worst, incur only minor embarrassment or financial setback. The next breach is coming—make it a boring one.
Take it from a guy who lost 35 iced coffees’ worth of rewards points and lived to tell the tale.



Wondering if Google has decided to re-think where they source the Titan hardware from. As recently as 2024, it was still Feitian, which doesn't seem optimal to source from the most likely state-based threat. https://x.com/joemosch/status/1250603461105729537
I’m so sorry you went through this. Thanks for writing this important piece with practical advice.